Hash values are unique identifiers for data integrity, while metadata provides contextual information about data. Both are crucial for legal compliance in evidence authentication.
Last Updated April 2024
One of the major challenges in handling digital evidence is the ease in which it can be altered, either intentionally or accidentally. Even simple actions like opening a file or copying a document can change its properties. Hash values mitigate this risk by providing a method to detect any changes. Similarly, metadata must be carefully preserved from the moment of capture to prevent any actions that could compromise the evidence’s reliability.
Hash values are unique digital fingerprints of data. Created by hash functions, these cryptographic strings represent the exact state of a digital file at the time of capture. Any alteration, no matter how minor, results in a completely different hash value. This characteristic makes hash values indispensable for verifying the integrity of digital evidence.
Metadata, on the other hand, refers to the data about data. It includes details such as the date and time a document was accessed, the device used, and the file format. In the context of online evidence, metadata can provide the background information necessary to establish the context and authenticity of the data.
The Federal Rules of Evidence require that material presented in court is authentic and unchanged. Hash values confirm that digital evidence remains intact since its collection. This capability is essential for complying with Rule 901(b)(9), which pertains to the authentication of a process or system producing an outcome.
Metadata also supports compliance with these rules by documenting the "when, where, and how" of evidence collection. This documentation helps establish a legal and ethical collection process, along with a clear timeline and chain of custody—key factors under Rules 901 and 902 for establishing evidence authenticity.
As such, screenshots alone are often deemed insufficient in court (as seen, for example, in Cristo v. Cayabyab). Without accompanying hash values and metadata, there is no intrinsic method to validate a screenshots’ integrity or to confirm it has remained unchanged since its capture.
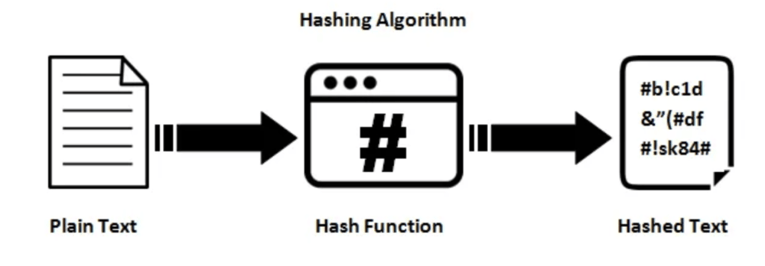
When collecting online evidence for court, it's essential to use reliable and secure cryptographic hash functions to ensure the integrity and authenticity of the data. Hash functions are algorithms that take an input (or 'message') and return a fixed-size string of bytes. The output, known as the hash value, should ideally be unique to each unique input.
Source: InfoSec Write Ups
❌ To Avoid
MD5 (Message Digest Algorithm 5): Once widely used, MD5 generates a 128-bit hash value. However, it is now considered to be less secure due to vulnerabilities that allow for potential collisions (different inputs producing the same output), thus is generally not recommended for legal use.
SHA-1 (Secure Hash Algorithm 1): Produces a 160-bit hash value. Similar to MD5, SHA-1 has also been found vulnerable to collision attacks and should be avoided in legal evidence contexts.
✅ Recommended
SHA-3: The latest member of the Secure Hash Algorithm family, SHA-3 is a subset of the cryptographic hash function originally called Keccak. It offers various digest sizes and is considered to be extremely secure. However, it might not be necessary for all contexts given its computational overhead and the adequate security provided by SHA-256.
SHA-256 (Secure Hash Algorithm 256-bit): Part of the SHA-2 family, this algorithm generates a 256-bit hash and is widely regarded as secure. It offers a good balance of speed and resistance to collisions, making it suitable for most current security applications. SHA-256 is highly recommended for legal and forensic purposes due to its robust security features. It is suitable for ensuring the integrity of online evidence as it significantly minimizes the risk of collisions.
For legal evidence collection, SHA-256 is generally the recommended hash function to use. It provides a strong level of security against collisions, is computationally efficient, and is supported by a wide range of software tools designed for digital forensics and legal evidence preservation. Using SHA-256 ensures that the hash values generated are both secure and reliable, which is crucial for maintaining the integrity of evidence throughout the legal process.
While a hash value confirms the integrity of data, metadata provides the contextual background necessary to interpret hash values. This context is vital for establishing the relevance and timing of the evidence in relation to the case. Here's an overview of the essential types of metadata for online evidence:
Legal professionals should prioritize using specialized software tools like Page Vault for online evidence collection due to its ability to handle crucial elements such as hash values and metadata, which are essential for maintaining the integrity and admissibility of social media and web evidence in court.
Page Vault automatically generates SHA-256 hash values for each piece of collected digital content, ensuring that the evidence remains unchanged from the point of capture to presentation in court. This feature is vital for proving that no tampering has occurred, meeting stringent legal standards for evidence integrity.
Additionally, Page Vault collects metadata, including timestamps, URL data, access information, and more which provide necessary context. This comprehensive data capture not only streamlines the process of evidence collection but also fortifies the evidence's credibility, greatly enhancing its legal standing and reducing the risk of challenges in court.
Due to its patented architecture, Page Vault keeps users out of the chain of custody and can provide affidavits for all captures made through its software or service.